A Secure Key Management Protocol guarantees the integrity of cryptographic keys throughout their lifecycle. This protocol adopts a set of procedures to create new keys, archive them securely, and transmit them effectively among authorized parties. The protocol in addition handles key replacement to reduce the threat of compromise.
Masked Communication Protocol 26b5a-1c56c-6125a-6ff89-6c087
The protocol 26b5a-1c56c-6125a-6ff89-6c087 is a novel method for sharing data in an secure manner. This sophisticated system utilizes algorithms to scramble information, making it legible only to authorized recipients. By employing robust security strategies, 26b5a-1c56c-6125a-6ff89-6c087 provides a reliable channel for private communication.
- Strengths of using 26b5a-1c56c-6125a-6ff89-6c087 include improved privacy, cybersecurity, and reduced risk of attacks.
- Implementations for this protocol are wide-ranging, spanning from personal communication to critical infrastructure.
Realization Details for 26b5a-1c56c-6125a-6ff89-6c087
This document outlines the comprehensive implementation parameters for the project identifier 26b5a-1c56c-6125a-6ff89-6c087. It provides a concise overview of the strategies employed, the technologies utilized, and the anticipated outcomes. The implementation process is documented in steps, each with its distinct objectives and outputs. Communication between stakeholders is vital throughout the implementation lifecycle to ensure a successful transition.
System Analysis of 26b5a-1c56c-6125a-6ff89-6c087 Robustness
The protocol 26b5a-1c56c-6125a-6ff89-6c087, a unique system for communicating sensitive data, requires thorough security analysis to confirm its integrity. This analysis will examine the protocol's architecture and identify potential vulnerabilities that could website be exploited by attackers. A multifaceted approach will be employed, including code review, to evaluate the protocol's protection against various attacks.
Furthermore, the analysis will consider real-world scenarios to highlight potential points of failure. The goal is to reduce the risk of security breaches and ensure the confidentiality, integrity, and availability of the data transmitted using this protocol.
Vulnerability Assessment for 26b5a-1c56c-6125a-6ff89-6c087
Performing a in-depth vulnerability assessment on the system with identifier 26b5a-1c56c-6125a-6ff89-6c087 is vital for identifying potential flaws. This analysis involves meticulously examining the system's design to uncover any vulnerabilities that could be leveraged by cybercriminals. By regularly conducting these assessments, organizations can reduce the risk of breaches, protecting their sensitive data and infrastructure.
Assessment for 26b5a-1c56c-6125a-6ff89-6c087
The detailed performance evaluation of the system 26b5a-1c56c-6125a-6ff89-6c087 reveals its capabilities in multiple domains. The analysis incorporated a variety of measures to assess its performance across significant parameters.
- Additionally, the outcomes indicate that the system exhibits efficient operation under varied scenarios.
- However, there are areas where optimization is required to maximize its comprehensive efficiency.
Mitigating these shortcomings will contribute in a more robust and effective application.
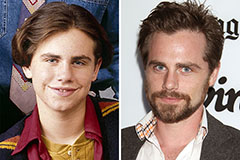 Rider Strong Then & Now!
Rider Strong Then & Now! Tia Carrere Then & Now!
Tia Carrere Then & Now! Christina Ricci Then & Now!
Christina Ricci Then & Now! Tonya Harding Then & Now!
Tonya Harding Then & Now! McKayla Maroney Then & Now!
McKayla Maroney Then & Now!